An Obscure Open Source AI Tool Alerted on Kelp DAO's $292 million Bug 12 Days Ago
Original Title: Kelp DAO's $292M Hack: What an AI Agent Caught 12 Days Early—and What It Means for DeFi Security
Original Source: Zengineer Blog
Original Translation: DeepTide TechFlow
DeepTide Summary: On April 18, Kelp DAO was hacked for $292 million, marking the largest DeFi incident of 2026. The exploit was not in the smart contract code but in the LayerZero cross-chain bridge's 1-of-1 verification node configuration—a single point of failure that could forge cross-chain messages.
The author had flagged this vulnerability 12 days prior while scanning Kelp with their custom AI auditing tool. This article retraces the attack process and also candidly reflects on three things the tool didn't get right at that time.
What is Kelp DAO
Kelp DAO is a liquidity redeposit protocol built on EigenLayer. The mechanism works as follows: Users deposit ETH or liquidity staked tokens (stETH, ETHx) into the Kelp contract, which then delegates the assets to EigenLayer's operator nodes for redeposit—providing security through multiple Actively Validated Services (AVS). In return, users receive rsETH as a claim.
Unlike direct staking on EigenLayer (where assets are locked), rsETH is liquid—tradeable, usable as collateral in protocols like Aave, and can also be used cross-chain.
To achieve this cross-chain liquidity, Kelp deployed rsETH on over 16 chains using LayerZero's Omnichain Fungible Token (OFT) standard. When you move rsETH from Ethereum to a particular L2 chain, LayerZero's Decentralized Verifier Network (DVN) validates whether this cross-chain message is legitimate. This bridge architecture is central to the events that unfolded.
Kelp, initiated by Amitej Gajjala and Dheeraj Borra (formerly co-founders of Stader Labs), launched in December 2023, reached a peak TVL of $20.9 billion, with governance using a 6/8 multisig plus a 10-day contract upgrade timelock. The governance token KERNEL oversees the Kelp, Kernel, and Gain product lines.
Theft Incident
On April 18, 2026, an attacker drained 116,500 rsETH from the Kelp DAO's cross-chain bridge, approximately $2.92 billion — the largest DeFi hack of 2026 to date. The root cause was not a smart contract vulnerability but a configuration issue: a 1-of-1 DVN setting (meaning only 1 validator node, with consensus reached by a single signature), allowing the attacker to spoof cross-chain messages with a single compromised node.
12 days earlier, on April 6, my open-source security auditing tool had already flagged this attack vector.
Let's start with this: This theft involved real people losing real money. The Aave WETH depositors who never interacted with rsETH had their funds frozen; LPs in multiple protocols are facing defaults they never agreed to take. This article analyzes what happened, what our tool detected — but the real-world cost to individuals is more significant than any scorecard.
The full report is posted on GitHub, with commit timestamps for anyone to verify. Below, we discuss what we caught, what we missed, and what this incident means for DeFi security tools.
46 Minutes, DeFi Shake-Up
At 17:35 UTC on April 18, the attacker compromised that isolated DVN validation node and had it "approve" a forged cross-chain message. LayerZero's Endpoint saw the DVN pass, relayed the message through lzReceive to Kelp's OFT contract — the contract complied, minting 116,500 rsETH on the Ethereum mainnet. The message claimed equivalent assets were locked on other chains as collateral. Those assets never existed.
Next is a standard DeFi money laundering process:
1. Deposit stolen rsETH as collateral into Aave V3, Compound V3, Euler
2. Borrow around $236 million worth of WETH using this uncollateralized collateral
3. Gather around 74,000 ETH, withdraw using Tornado Cash
At 18:21, 46 minutes later, Kelp's emergency pause multisig froze the contract. The attacker then front-run twice (40,000 rsETH each, around $100 million) all reverted—blocking around $200 million more this time.
However, the aftermath was brutal. Aave V3 suffered approximately $177 million in defaults. The AAVE token plummeted by 10.27%. ETH dropped by 3%. The utilization rate of WETH on Aave instantly maxed out at 100%, with depositors rushing to withdraw. rsETH on over 20 L2s overnight turned into assets of questionable value.
April 6 Report Findings
In early April, shortly after the $285 million theft of Drift Protocol on April 1, I authored an open-source Claude Code skill crypto-project-security-skill—an AI-assisted architecture risk assessment framework that evaluates DeFi protocols using public data (DeFiLlama, GoPlus, Safe API, on-chain verification). It is not a code scanner or formal verification tool.
The Drift incident made me realize: the primary cause of the greatest losses is not in the smart contract code but in governance vulnerabilities, configuration oversights, architectural blind spots, areas invisible to code scanners. Consequently, I developed a tool specifically to assess these layers: governance structure, oracle dependencies, economic mechanisms, cross-chain architecture, comparing each protocol to attack patterns from famous historical attacks (Drift, Euler, Ronin, Harmony, Mango).
On April 6, I conducted a comprehensive audit of Kelp DAO. The full report is publicly available on GitHub with an immutable commit timestamp.
The overall triage score reported to Kelp is 72/100 (Medium Risk). In hindsight, this score was too lenient—the several unanswered cross-chain information gaps should have brought the score down. But even under a Medium Risk rating, the report highlighted the attack surface that was later exploited.
The screenshot below shows the original text of the "Information Gap" section of the report—about the issue with Kelp's DVN configuration, which ultimately led to a $292 million theft:
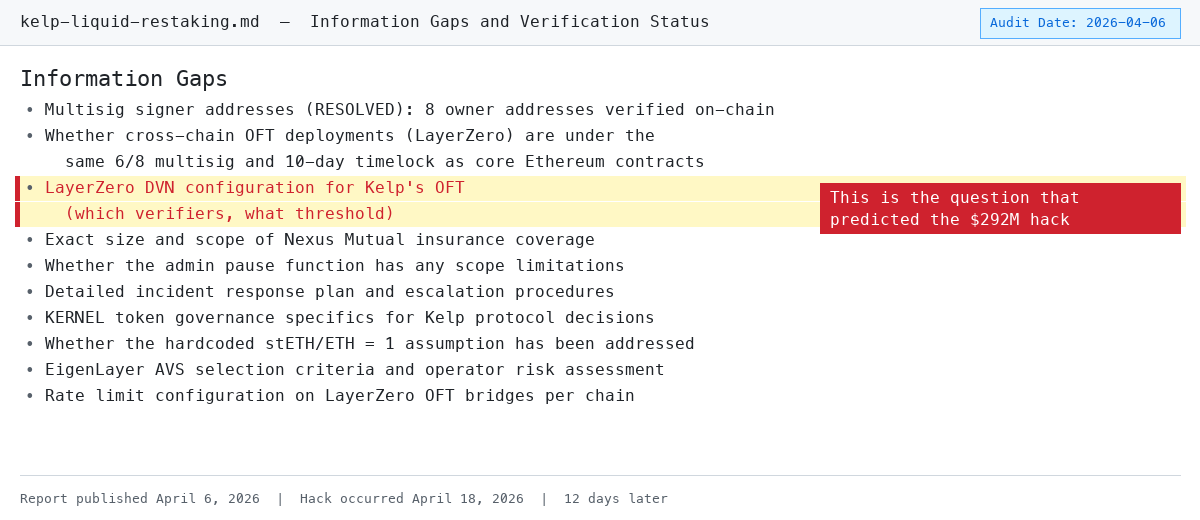
The "Information Gap" section of the report from April 6 directly called out the lack of transparency in the DVN configuration
The following compares each marked item in the report with how it was actually breached.
Discovery 1: Non-transparent DVN Configuration (Early Warning)
Reported Text: "LayerZero DVN configuration (validator sets for each chain, threshold requirements) not publicly disclosed"
What Actually Happened: Kelp was running a 1-of-1 DVN configuration. One node. One single point. By compromising this single node, the attacker falsified cross-chain messages. If the configuration had been 2-of-3 (industry minimum recommendation), the attacker would have had to breach multiple independent validators simultaneously.
Let's be clear about one thing: this is Kelp's issue, not LayerZero's. LayerZero is the infrastructure—it provides the DVN framework, and each protocol chooses its configuration: how many validator nodes (1-of-1, 2-of-3, 3-of-5...), whose nodes to use, and the threshold for each chain. When deploying the OFT bridge, Kelp chose 1-of-1. LayerZero fully supports 2-of-3 or higher—it's Kelp's own decision not to utilize it.
For example: AWS offers MFA (multi-factor authentication). If your account is compromised because you never enabled MFA, that's your issue, not AWS's. LayerZero has the security measures in place, but Kelp didn't use them.
At the time of our report, we couldn't determine the specific DVN threshold (because Kelp had never disclosed it), but we clearly listed this lack of transparency as an unresolved information gap and a risk item. Non-disclosure itself is a red flag.
Finding 2: Single Point of Failure Across 16 Chains (Direct Hit)
Original Report: "LayerZero DVN's single point of failure, potentially impacting 16 chains supporting rsETH on-chain."
What Actually Happened: A forged message directly hit the Ethereum mainnet, causing a ripple effect across all chains with rsETH deployment. LayerZero proactively paused all outbound OFT bridges from Ethereum. Holders of rsETH on over 20 L2s found themselves unsure overnight whether their tokens were still backed.
This represents a systemic risk of multi-chain deployment: rsETH circulates on multiple L2s such as Arbitrum, Optimism, Base, and Scroll, but the value of all these tokens is derived from assets on the Ethereum mainnet. With the mainnet bridge compromised, rsETH on each L2 lost its backing simultaneously—holders were unable to redeem and couldn't verify if their tokens were still valuable. Lido's earnETH (holding rsETH exposure) and Ethena's LayerZero bridge—both were forced to halt operations. The blast radius extended far beyond Kelp itself.
Finding 3: Unverified Cross-Chain Governance Control (Related Issue)
Original Report: "Unverified governance control over the LayerZero OFT configurations across chains—specifically, whether this control belongs to the same 6/8 multisig and 10-day timelock, or is managed by independent admin keys."
What Actually Happened: The DVN configuration evidently does not fall under the strict governance of the core protocol. If bridge configuration changes are also governed by a 6/8 multisig and 10-day timelock, the 1-of-1 DVN setting would require agreement from 6 out of 8 signers—such a setup is unlikely to remain unattended.
This exposes a common governance blind spot: while many protocols have strict multisig plus timelock setups for core contract upgrades, operational changes—such as bridge configurations, oracle parameters, and whitelist management—often rely on a single admin key for alterations. Kelp's core protocol governance is best-in-class (6/8 multisig + 10-day timelock), but these protections do not extend to its largest attack surface: cross-chain bridges.
Discovery 4: Matching Ronin/Harmony Attack Pattern (Direct Hit)
Original Report: "The most relevant historical precedent involves bridge security. Kelp's LayerZero deployment across 16 chains brought operational complexity similar to Ronin's multi-chain architecture."
What Actually Happened: The attack path almost perfectly replicated the Ronin script—breaching the bridge validators, forging messages, and draining assets. Our tool's attack pattern matching module compared the protocol architecture and historical attack categories, correctly identifying this as the highest-risk attack vector.
Historical Context: In 2022, the Ronin bridge suffered a $625 million loss from 5 out of 9 validators being breached; in the same year, Harmony's Horizon bridge lost $100 million from 2 out of 5 validators being breached.
Kelp's situation was even more extreme—with only 1 validator, pushing the attack threshold to the absolute minimum. The reason the tool was able to flag this risk is because it automatically compares the protocol architecture to these historical attack patterns, rather than just looking at the code.
Discovery 5: Lack of Insurance Pool (Amplifying Losses)
Original Report: "The protocol currently does not have a dedicated insurance pool, nor a socialized loss absorption mechanism to absorb forfeiture events."
What Actually Happened: Due to the absence of an insurance reserve, the $292 million loss was entirely absorbed by the downstream protocol. Aave's recovery reserve covered only 30% of its $177 million default. LPs unrelated to Kelp bridge configuration bore the brunt of the impact.
The attacker used the stolen rsETH as collateral, deposited into Aave V3, Compound V3, and Euler, then borrowed real WETH. Once the rsETH was confirmed as unsecured, these positions became "unrecoverable" defaults—collateral turned to waste paper, but the borrowed WETH was already gone. WETH utilization on Aave instantly maxed out, preventing even regular users from withdrawing. If you are a WETH depositor on Aave, even if you never touched rsETH, your funds are affected. The insurance partnership between Kelp and Nexus Mutual only covered specific treasury products, not the core rsETH protocol exposure.
This is a case of both parties failing to fulfill their responsibilities. On the Kelp side: a protocol with a TVL of $1.3 billion, zero insurance pool, and zero loss absorption mechanism. When the bridge was compromised, there was no buffer to absorb the damage. On the Aave side: accepting rsETH as collateral without adequately assessing the cross-chain bridge configuration risk.
Aave's risk parameters (LTV, liquidation threshold) were designed for normal price fluctuations but did not consider the tail risk of "bridge configuration compromise leading to collateral wipeout" scenario. Even a 30% recovery reserve cannot cover such a scenario. Essentially, this was a risk pricing failure: Aave treated rsETH as a normal fluctuating asset, but it actually carried a binary tail risk of bridge failure. The failures on both sides compounded — Kelp failed to have insurance to prevent bad collateral from entering the system, and Aave failed to perform sufficiently granular risk modeling to limit exposure in this scenario.
Where We Went Wrong
Three things should have been done better:
Underestimation of Risk Rating. We rated the cross-chain bridge risk as "medium." Out of 5 unresolved information gaps in the report, 3 were related to LayerZero bridge configuration, matching the historical attack pattern of Ronin/Harmony — this should have been rated as "high" or "critical." Opacity itself should have been a stronger signal.
We Failed to Penetrate the Configuration Layer. The report repeatedly asked Kelp to disclose the DVN threshold, but we could not verify independently. This is the same structural blind spot highlighted by The Block's post-mortem analysis: existing audit tools focus on code logic and miss risks in the configuration layer. We flagged the issue but could not answer it.
We Did Not Verify On-Chain. The DVN configuration could actually be read on-chain directly via LayerZero's EndpointV2 contract. We could have queried the ULN302 registry to independently confirm Kelp's DVN threshold instead of labeling it "undisclosed." If we had checked then, we would have directly seen the 1-of-1 configuration without needing Kelp's disclosure. This is the most specific improvement direction for tools: adding on-chain DVN configuration verification to the cross-chain assessment process.
Discovery was not specific enough, not actionable enough. Saying "DVN configuration not disclosed" was observing a documentation gap — not predicting an attack. These risks (oracle centralization, bridge reliance, lack of insurance) are actually equally prevalent in most cross-chain DeFi protocols. The tool flagged Kelp's opacity, but it has also marked similar patterns on dozens of protocols that have not been attacked. Without disclosing the false positive rate, claiming "we predicted it" is an exaggeration of the facts. A more honest statement would be: we asked some correct questions that nobody else was asking, and one of them happened to touch on a critical weak point.
About "Responsible Disclosure"
A Fair Question: If we identified these risks on April 6, why didn't we notify Kelp before the attack on April 18?
No notification. The reason is: The report identified an opacity—"DVN Configuration Not Disclosed"—not a specific exploitable vulnerability. We did not know the configuration was 1-of-1, only that it was not public. There was nothing specific enough to disclose. "Your bridge configuration is undocumented" was a governance observation, not a report suitable for a bug bounty program submission.
In hindsight, we could have directly contacted the Kelp team to inquire about their DVN threshold. That conversation might have exposed the 1-of-1 configuration and led to a fix. We did not. This is a lesson: Even if a discovery seems too vague for a formal disclosure process, it is still worthwhile to privately message and ask a question.
What This Means for DeFi Security
Kelp's theft—like Drift's theft 17 days ago—is not due to a smart contract bug. Automated code scanners like Slither, Mythril, or even GoPlus cannot catch it. The vulnerability lies in deployment configurations, governance gaps, and architectural decisions, above the code layer.
This is also the core tenet of crypto-project-security-skill:
Protocol security is not just code security. A protocol can have flawless Solidity, five audits from top firms, a $250,000 bug bounty—and still lose $292 million due to a bridge validator configuration issue.
The tools are open-source on GitHub—anyone can review the methodology, run it themselves, or improve it.
Timeline
12 days. The signals were there long ago. The question is: How should the ecosystem establish tools that can see these signals before the next bridge collapses?
What You Can Do
If you have assets in a DeFi protocol with a bridged cross-chain bridge:
1. Conduct a Self-Audit. The tool is open source. Don't trust, verify.
2. Check Bridge Validator Configuration. If a protocol is unwilling to disclose its DVN threshold, consider it a red flag. That's exactly what our report did, and it proved to be right.
3. Don't Assume Code Audits Cover Everything. Kelp has undergone more than 5 code audits from well-known companies and platforms (Code4rena, SigmaPrime, MixBytes). Traditional code audits are not designed to capture configuration layer risks such as DVN threshold settings — that is a different analysis and not a fault of the audit firms.
4. Evaluate Insurance Coverage. If a protocol does not have an insurance pool, and you are an LP on a lending platform that accepts its token as collateral, you are implicitly underwriting it. The Aave incident with WETH depositors learned this the hard way.
The Bigger Picture: AI Agent as a Security Layer
This article discusses a tool and a hack. But the underlying proposition is larger: AI Agent can be an independent security layer for DeFi investors.
The traditional security model in the crypto industry looks like this: protocol hires an audit firm, audit firm reviews the code, audit firm publishes a report. This model has blind spots — as demonstrated by the Kelp incident, it focuses on code correctness but overlooks configuration, governance, and architectural risks.
What Claude Code and similar tools bring is another path: anyone can run an AI-assisted risk assessment on any protocol using publicly available data in minutes. You don't need to spend $200,000 on an audit firm. You don't need to know how to read Solidity. You let the agent compare the protocol architecture to known attack patterns, and it presents you with the questions you should be asking before depositing funds.
This doesn't replace professional audits — but it lowers the due diligence barrier of the first layer to a level where anyone can use it. An LP considering allocating funds to a new staking protocol can now run a DeFi audit.
The Kelp report was not perfect. It rated the bridge risk as medium when it should have been severe. It did not delve into the configuration layer. But it asked the right questions — if the Kelp team or any LP had taken these questions seriously at the time, the $292 million loss could have been avoided.
Original Article Link
You may also like

Why can this institution still grow by 150% when the scale of leading crypto VCs has shrunk significantly?

Anthropic's $1 trillion, compared to DeepSeek's $100 billion

Geopolitical Risk Persists, Is Bitcoin Becoming a Key Barometer?

Annualized 11.5%, Wall Street Buzzing: Is MicroStrategy's STRC Bitcoin's Savior or Destroyer?

Mixin has launched USTD-margined perpetual contracts, bringing derivative trading into the chat scene.
The privacy-focused crypto wallet Mixin announced today the launch of its U-based perpetual contract (a derivative priced in USDT). Unlike traditional exchanges, Mixin has taken a new approach by "liberating" derivative trading from isolated matching engines and embedding it into the instant messaging environment.
Users can directly open positions within the app with leverage of up to 200x, while sharing positions, discussing strategies, and copy trading within private communities. Trading, social interaction, and asset management are integrated into the same interface.
Based on its non-custodial architecture, Mixin has eliminated friction from the traditional onboarding process, allowing users to participate in perpetual contract trading without identity verification.
The trading process has been streamlined into five steps:
· Choose the trading asset
· Select long or short
· Input position size and leverage
· Confirm order details
· Confirm and open the position
The interface provides real-time visualization of price, position, and profit and loss (PnL), allowing users to complete trades without switching between multiple modules.
Mixin has directly integrated social features into the derivative trading environment. Users can create private trading communities and interact around real-time positions:
· End-to-end encrypted private groups supporting up to 1024 members
· End-to-end encrypted voice communication
· One-click position sharing
· One-click trade copying
On the execution side, Mixin aggregates liquidity from multiple sources and accesses decentralized protocol and external market liquidity through a unified trading interface.
By combining social interaction with trade execution, Mixin enables users to collaborate, share, and execute trading strategies instantly within the same environment.
Mixin has also introduced a referral incentive system based on trading behavior:
· Users can join with an invite code
· Up to 60% of trading fees as referral rewards
· Incentive mechanism designed for long-term, sustainable earnings
This model aims to drive user-driven network expansion and organic growth.
Mixin's derivative transactions are built on top of its existing self-custody wallet infrastructure, with core features including:
· Separation of transaction account and asset storage
· User full control over assets
· Platform does not custody user funds
· Built-in privacy mechanisms to reduce data exposure
The system aims to strike a balance between transaction efficiency, asset security, and privacy protection.
Against the background of perpetual contracts becoming a mainstream trading tool, Mixin is exploring a different development direction by lowering barriers, enhancing social and privacy attributes.
The platform does not only view transactions as execution actions but positions them as a networked activity: transactions have social attributes, strategies can be shared, and relationships between individuals also become part of the financial system.
Mixin's design is based on a user-initiated, user-controlled model. The platform neither custodies assets nor executes transactions on behalf of users.
This model aligns with a statement issued by the U.S. Securities and Exchange Commission (SEC) on April 13, 2026, titled "Staff Statement on Whether Partial User Interface Used in Preparing Cryptocurrency Securities Transactions May Require Broker-Dealer Registration."
The statement indicates that, under the premise where transactions are entirely initiated and controlled by users, non-custodial service providers that offer neutral interfaces may not need to register as broker-dealers or exchanges.
Mixin is a decentralized, self-custodial privacy wallet designed to provide secure and efficient digital asset management services.
Its core capabilities include:
· Aggregation: integrating multi-chain assets and routing between different transaction paths to simplify user operations
· High liquidity access: connecting to various liquidity sources, including decentralized protocols and external markets
· Decentralization: achieving full user control over assets without relying on custodial intermediaries
· Privacy protection: safeguarding assets and data through MPC, CryptoNote, and end-to-end encrypted communication
Mixin has been in operation for over 8 years, supporting over 40 blockchains and more than 10,000 assets, with a global user base exceeding 10 million and an on-chain self-custodied asset scale of over $1 billion.

$600 million stolen in 20 days, ushering in the era of AI hackers in the crypto world

Vitalik's 2026 Hong Kong Web3 Summit Speech: Ethereum's Ultimate Vision as the "World Computer" and Future Roadmap

On the same day Aave introduced rsETH, why did Spark decide to exit?

Full Post-Mortem of the KelpDAO Incident: Why Did Aave, Which Was Not Compromised, End Up in Crisis Situation?

After a $290 million DeFi liquidation, is the security promise still there?

ZachXBT's post ignites RAVE nearing zero, what is the truth behind the insider control?

Vitalik 2026 Hong Kong Web3 Carnival Speech Transcript: We do not compete on speed; security and decentralization are the core

In-depth Analysis of RAVE Events: Short Squeeze, Crash, and Quantitative Financial Models of Liquidity Manipulation

Eve of Ceasefire, US Military Fires on Iranian Vessel | Rewire News Morning Brief

Figma's stock price drops over 7%, will Claude Design be the terminator?

Plunge by 10% Followed by Rebound, Weekend Oil Market Watch

SpaceX Mascot ASTEROID Fast Track $170 million, Stemming from an Unfinished Space Dream

L1 is dead, Appchain should rise
Why can this institution still grow by 150% when the scale of leading crypto VCs has shrunk significantly?
Anthropic's $1 trillion, compared to DeepSeek's $100 billion
Geopolitical Risk Persists, Is Bitcoin Becoming a Key Barometer?
Annualized 11.5%, Wall Street Buzzing: Is MicroStrategy's STRC Bitcoin's Savior or Destroyer?
Mixin has launched USTD-margined perpetual contracts, bringing derivative trading into the chat scene.
The privacy-focused crypto wallet Mixin announced today the launch of its U-based perpetual contract (a derivative priced in USDT). Unlike traditional exchanges, Mixin has taken a new approach by "liberating" derivative trading from isolated matching engines and embedding it into the instant messaging environment.
Users can directly open positions within the app with leverage of up to 200x, while sharing positions, discussing strategies, and copy trading within private communities. Trading, social interaction, and asset management are integrated into the same interface.
Based on its non-custodial architecture, Mixin has eliminated friction from the traditional onboarding process, allowing users to participate in perpetual contract trading without identity verification.
The trading process has been streamlined into five steps:
· Choose the trading asset
· Select long or short
· Input position size and leverage
· Confirm order details
· Confirm and open the position
The interface provides real-time visualization of price, position, and profit and loss (PnL), allowing users to complete trades without switching between multiple modules.
Mixin has directly integrated social features into the derivative trading environment. Users can create private trading communities and interact around real-time positions:
· End-to-end encrypted private groups supporting up to 1024 members
· End-to-end encrypted voice communication
· One-click position sharing
· One-click trade copying
On the execution side, Mixin aggregates liquidity from multiple sources and accesses decentralized protocol and external market liquidity through a unified trading interface.
By combining social interaction with trade execution, Mixin enables users to collaborate, share, and execute trading strategies instantly within the same environment.
Mixin has also introduced a referral incentive system based on trading behavior:
· Users can join with an invite code
· Up to 60% of trading fees as referral rewards
· Incentive mechanism designed for long-term, sustainable earnings
This model aims to drive user-driven network expansion and organic growth.
Mixin's derivative transactions are built on top of its existing self-custody wallet infrastructure, with core features including:
· Separation of transaction account and asset storage
· User full control over assets
· Platform does not custody user funds
· Built-in privacy mechanisms to reduce data exposure
The system aims to strike a balance between transaction efficiency, asset security, and privacy protection.
Against the background of perpetual contracts becoming a mainstream trading tool, Mixin is exploring a different development direction by lowering barriers, enhancing social and privacy attributes.
The platform does not only view transactions as execution actions but positions them as a networked activity: transactions have social attributes, strategies can be shared, and relationships between individuals also become part of the financial system.
Mixin's design is based on a user-initiated, user-controlled model. The platform neither custodies assets nor executes transactions on behalf of users.
This model aligns with a statement issued by the U.S. Securities and Exchange Commission (SEC) on April 13, 2026, titled "Staff Statement on Whether Partial User Interface Used in Preparing Cryptocurrency Securities Transactions May Require Broker-Dealer Registration."
The statement indicates that, under the premise where transactions are entirely initiated and controlled by users, non-custodial service providers that offer neutral interfaces may not need to register as broker-dealers or exchanges.
Mixin is a decentralized, self-custodial privacy wallet designed to provide secure and efficient digital asset management services.
Its core capabilities include:
· Aggregation: integrating multi-chain assets and routing between different transaction paths to simplify user operations
· High liquidity access: connecting to various liquidity sources, including decentralized protocols and external markets
· Decentralization: achieving full user control over assets without relying on custodial intermediaries
· Privacy protection: safeguarding assets and data through MPC, CryptoNote, and end-to-end encrypted communication
Mixin has been in operation for over 8 years, supporting over 40 blockchains and more than 10,000 assets, with a global user base exceeding 10 million and an on-chain self-custodied asset scale of over $1 billion.







